Other Articles
- EC2 Volume – Enable EBS Encryption
- EC2 Volume – Enable EBS Volume Backup
- EFS – Enable EFS Storage Backup
- EC2 Instance – Enable Deletion Protection
- EC2 Instance – Monitor CPU Utilization
- ECS Service – Monitor CPU Utilization
- ECS Service – Monitor Memory Utilization
- EC2 VPC – Ensure Flow Logs are Enabled
- S3 Bucket – Block S3 Bucket Public Access
- S3 Bucket – Enable S3 Bucket Versioning
- S3 Bucket – Enable S3 Bucket Encryption
- RDS DB Instance – Enable Auto Minor Version Upgrade
- RDS DB Instance – Block Public Access
- RDS DB Instance – Monitor Free Storage Space
- RDS DB Instance – Encryption of Storage
- RDS DB Instance – Enable Deletion Protection
- SQS Queue – Monitor Message Age
- SQS Queue – Monitor Message Visibility
- DynamoDB Table – Enable Table Encryption
- DynamoDB Table – Enable Table Point In Time Recovery
- DynamoDB Table – Enable Table Deletion Protection
- DynamoDB Table – Monitor Table Read Capacity
- DynamoDB Table – Monitor Table Write Capacity
- DynamoDB Table – Monitor Table Latency
- Enable User MFA
- Enforce Key Rotation
- Enforce Active Key Limit
- Disable Unused User Credentials
- Enforce Group Permission
- Enable CloudTrail
- Enable AWS Security Hub
- Enforce Password Length
- Prohibit Password Reuse
- Purge Expired Certificates
- Check Root Access Keys Existence
- Enable Root MFA
- Establish Support Role
- Enable Key Rotation
- Encrypt CloudTrail Logs
- Enable GuardDuty
RDS DB Instance – Monitor CPU Utilization
This check ensures that CPU utilization is actively monitored for Amazon RDS database instances. Monitoring CPU usage helps detect performance bottlenecks, prevent outages, and plan capacity effectively.
Check Details
- Resource: RDS DB Instance
- Check: Monitor RDS DB CPU utilization
- Risk: High CPU usage may cause slow queries, timeouts, or service downtime
Remediation via AWS Console
-
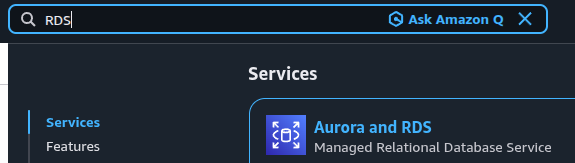
Log in to the AWS Management Console and open the
Amazon RDS console.
- In the left navigation pane, click Databases and select the affected RDS DB instance.
-
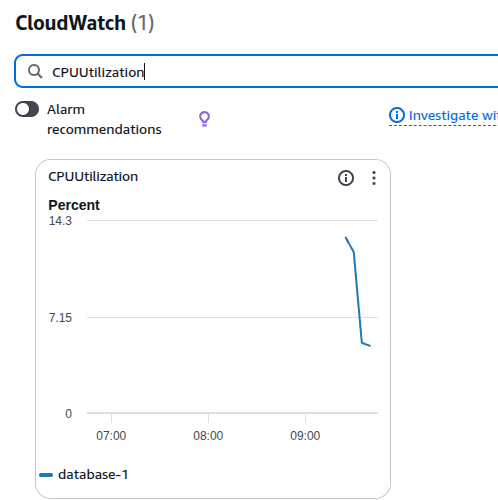
Open the Monitoring tab and search for
CPUUtilization.
-
If enhanced monitoring is disabled:
- Click Modify
- Enable Enhanced monitoring
- Select an appropriate monitoring interval
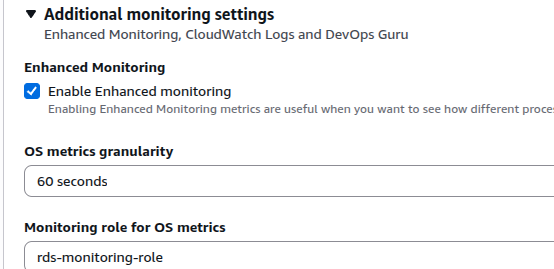
- Click Save changes.
Remediation via AWS CLI
-
Log in to the AWS Management Console and click the
CloudShell icon (
>_) in the top-right corner.
-
Enable enhanced monitoring for the RDS DB instance:
aws rds modify-db-instance \ --db-instance-identifier <db-instance-id> \ --monitoring-interval 60 \ --monitoring-role-arn <iam-role-arn> \ --apply-immediately
Replace <db-instance-id> and <iam-role-arn>
with the actual RDS DB instance identifier and IAM role ARN.