Other Articles
- IAM - Enable User MFA
- IAM - Enforce Key Rotation
- IAM - Enforce Active Key Limit
- IAM - Disable Unused User Credentials
- IAM - Enforce Group Permission
- IAM - Enforce Password Length
- IAM - Check Root Access Keys Existence
- IAM - Enable Root MFA
- IAM - Establish Support Role
- IAM - Enable Key Rotation
- Purge Expired Certificates
- EC2 Volume – Enable EBS Volume Backup
- EC2 Volume – Enable EBS Encryption
- EFS – Enable EFS Storage Backup
- S3 Bucket – Enable S3 Bucket Versioning
- S3 Bucket – Enable S3 Bucket Encryption
- S3 Bucket – Block S3 Bucket Public Access
- RDS DB Instance – Encryption of Storage
- RDS DB Instance – Enable Deletion Protection
- RDS DB Instance – Enable Auto Minor Version Upgrade
- DynamoDB Table – Enable Table Encryption
- DynamoDB Table – Enable Table Point In Time Recovery
- DynamoDB Table – Enable Table Deletion Protection
- EC2 Instance – Monitor CPU Utilization
- ECS Service – Monitor CPU Utilization
- ECS Service – Monitor Memory Utilization
- RDS DB Instance – Monitor Free Storage Space
- RDS DB Instance – Monitor CPU Utilization
- SQS Queue – Monitor Message Age
- SQS Queue – Monitor Message Visibility
- DynamoDB Table – Monitor Table Read Capacity
- DynamoDB Table – Monitor Table Write Capacity
- DynamoDB Table – Monitor Table Latency
- Enable CloudTrail
- Encrypt CloudTrail Logs
- EC2 VPC – Ensure Flow Logs are Enabled
- RDS DB Instance – Block Public Access
- EC2 Instance – Enable Deletion Protection
- ECS Service – Enable Auto Scaling
- Enable AWS Security Hub
- Enable GuardDuty
IAM - Prohibit Password Reuse
Secure Configuration Checks > AWS
This check ensures that IAM users cannot reuse previously used passwords. Preventing password reuse strengthens account security and reduces the risk of compromised credentials being reused.
Check Details
- Resource: General
- Check: Prohibit password reuse
- Risk: Reused passwords increase the risk of account compromise
Remediation via AWS Console
-
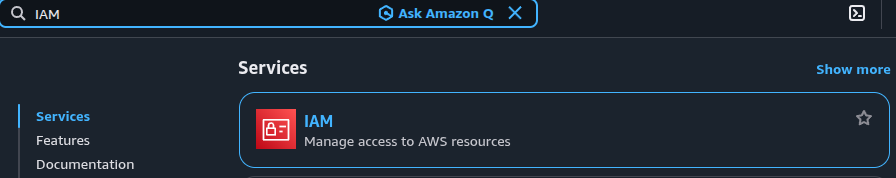
Log in to the AWS Management Console and open the IAM console.
-
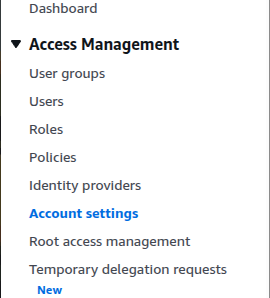
In the left navigation panel, select Account settings.
- Under Password policy, click Edit.
- Choose Custom password policy.
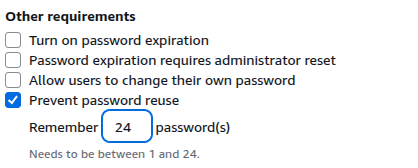
- Enable Prevent password reuse.
-
Set Number of passwords to remember to 24.
- Click Save changes.
Remediation via AWS CLI
-
Log in to the AWS Management Console and click the CloudShell icon (
>_) in the top-right corner.
-
Update the account password policy to prevent password reuse:
aws iam update-account-password-policy \ --password-reuse-prevention 24
Updated on 06 March, 2026