Other Articles
- EC2 Volume – Enable EBS Encryption
- EC2 Volume – Enable EBS Volume Backup
- EFS – Enable EFS Storage Backup
- EC2 Instance – Enable Deletion Protection
- EC2 Instance – Monitor CPU Utilization
- ECS Service – Monitor CPU Utilization
- ECS Service – Monitor Memory Utilization
- EC2 VPC – Ensure Flow Logs are Enabled
- S3 Bucket – Block S3 Bucket Public Access
- S3 Bucket – Enable S3 Bucket Versioning
- S3 Bucket – Enable S3 Bucket Encryption
- RDS DB Instance – Enable Auto Minor Version Upgrade
- RDS DB Instance – Block Public Access
- RDS DB Instance – Monitor Free Storage Space
- RDS DB Instance – Monitor CPU Utilization
- RDS DB Instance – Encryption of Storage
- RDS DB Instance – Enable Deletion Protection
- SQS Queue – Monitor Message Age
- SQS Queue – Monitor Message Visibility
- DynamoDB Table – Enable Table Encryption
- DynamoDB Table – Enable Table Point In Time Recovery
- DynamoDB Table – Enable Table Deletion Protection
- DynamoDB Table – Monitor Table Read Capacity
- DynamoDB Table – Monitor Table Write Capacity
- DynamoDB Table – Monitor Table Latency
- Enable User MFA
- Enforce Key Rotation
- Enforce Active Key Limit
- Disable Unused User Credentials
- Enforce Group Permission
- Enable CloudTrail
- Enable AWS Security Hub
- Enforce Password Length
- Prohibit Password Reuse
- Purge Expired Certificates
- Check Root Access Keys Existence
- Enable Root MFA
- Enable Key Rotation
- Encrypt CloudTrail Logs
- Enable GuardDuty
Establish Support Role
This check ensures that an IAM role with AWS Support permissions is established. A dedicated support role allows authorized users to manage AWS support cases securely without granting excessive permissions.
Check Details
- Resource: General
- Check: Establish support role
- Risk: Inability to manage AWS support incidents securely
Remediation via AWS Console
-
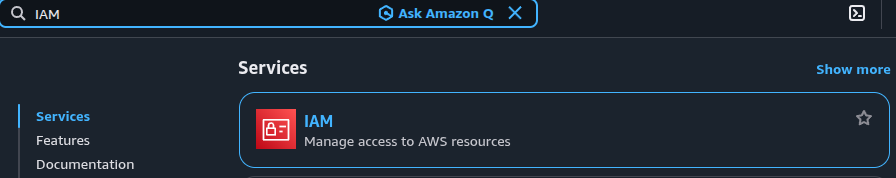
Log in to the AWS Management Console and open the
IAM service.
-
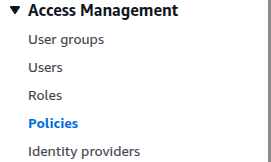
Under Access management, click Policies.
-
In the policy search field, search for
AWSSupportAccess.
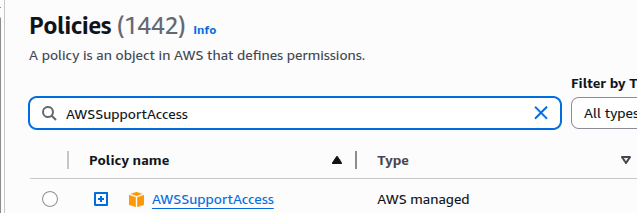
- Click the policy name AWSSupportAccess.
-
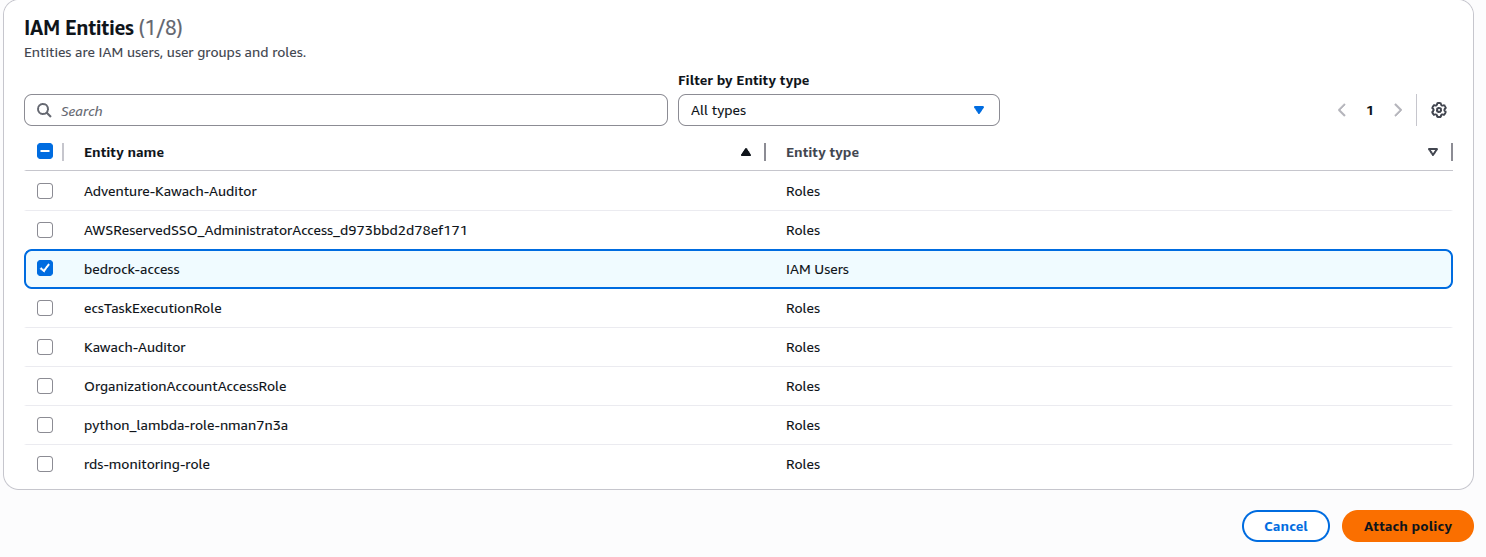
Open the Entities attached tab and click
Attach.
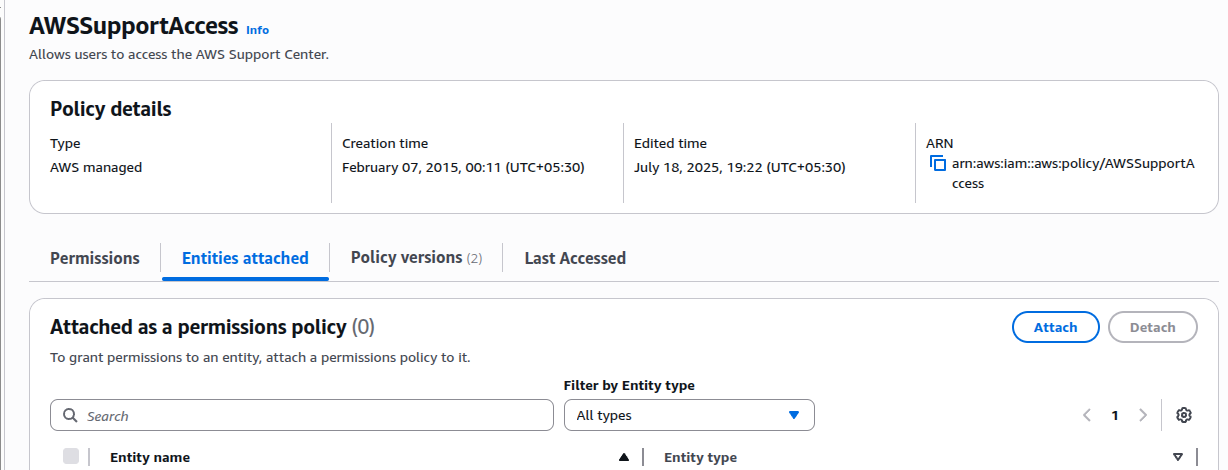
-
Select the appropriate IAM role or roles and click
Attach policy.
Remediation via AWS CLI
-
Log in to the AWS Management Console and click the
CloudShell icon (
>_) in the top-right corner.
-
Create a trust policy file:
Replacenano /tmp/TrustPolicy.json<iam_user>with the IAM user ARN and paste:
Press CTRL + O → Enter → CTRL + X.{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<iam_user>" }, "Action": "sts:AssumeRole" } ] } -
Create the IAM role:
aws iam create-role \ --role-name <aws_support_iam_role> \ --assume-role-policy-document file:///tmp/TrustPolicy.json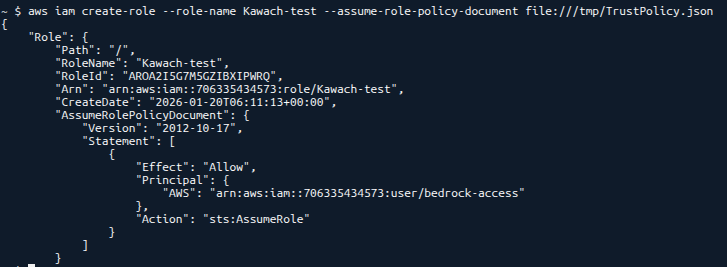
-
Attach AWS Support permissions to the role:
aws iam attach-role-policy \ --policy-arn arn:aws:iam::aws:policy/AWSSupportAccess \ --role-name <aws_support_iam_role> -
Verify the role has the required policy attached:
aws iam list-attached-role-policies \ --role-name <aws_support_iam_role>