Other Articles
- EC2 Volume – Enable EBS Encryption
- EC2 Volume – Enable EBS Volume Backup
- EFS – Enable EFS Storage Backup
- EC2 Instance – Enable Deletion Protection
- EC2 Instance – Monitor CPU Utilization
- ECS Service – Monitor CPU Utilization
- ECS Service – Monitor Memory Utilization
- EC2 VPC – Ensure Flow Logs are Enabled
- S3 Bucket – Block S3 Bucket Public Access
- S3 Bucket – Enable S3 Bucket Versioning
- S3 Bucket – Enable S3 Bucket Encryption
- RDS DB Instance – Enable Auto Minor Version Upgrade
- RDS DB Instance – Block Public Access
- RDS DB Instance – Monitor Free Storage Space
- RDS DB Instance – Monitor CPU Utilization
- RDS DB Instance – Encryption of Storage
- RDS DB Instance – Enable Deletion Protection
- SQS Queue – Monitor Message Age
- SQS Queue – Monitor Message Visibility
- DynamoDB Table – Enable Table Encryption
- DynamoDB Table – Enable Table Point In Time Recovery
- DynamoDB Table – Enable Table Deletion Protection
- DynamoDB Table – Monitor Table Read Capacity
- DynamoDB Table – Monitor Table Write Capacity
- DynamoDB Table – Monitor Table Latency
- Enable User MFA
- Enforce Key Rotation
- Enforce Active Key Limit
- Disable Unused User Credentials
- Enforce Group Permission
- Enable CloudTrail
- Enforce Password Length
- Prohibit Password Reuse
- Purge Expired Certificates
- Check Root Access Keys Existence
- Enable Root MFA
- Establish Support Role
- Enable Key Rotation
- Encrypt CloudTrail Logs
- Enable GuardDuty
Enable AWS Security Hub
This check ensures that AWS Security Hub is enabled for the account. Security Hub provides a centralized view of security alerts and compliance status across AWS services, helping teams identify and remediate security issues quickly.
Check Details
- Resource: General
- Check: Enable AWS Security Hub
- Risk: Security findings and compliance issues may go undetected
Remediation via AWS Console
- Sign in to the AWS Management Console using an IAM user or role with permissions for AWS Security Hub.
-
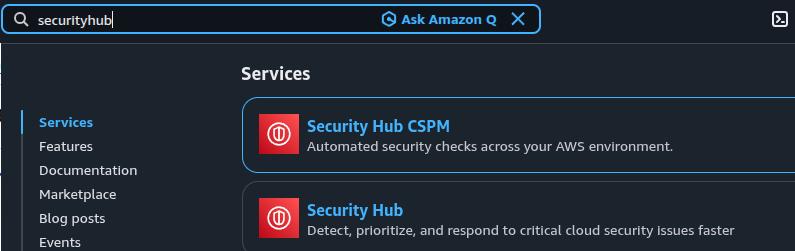
Open the AWS Security Hub console.
- If this is the first time opening Security Hub, choose Go to Security Hub.
-
In the Security standards section, review the available
standards and check the box for the standards you want to enable.
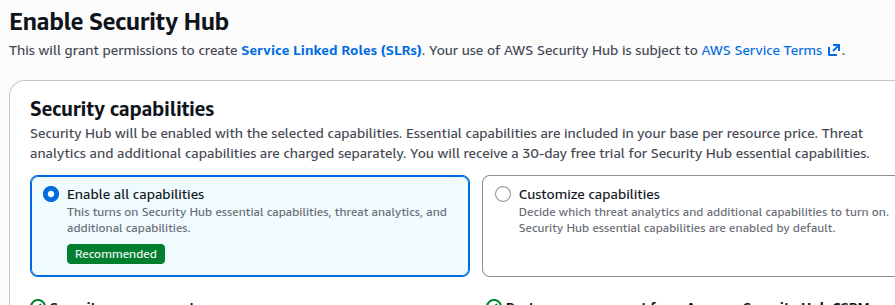
- Choose Enable Security Hub.
Remediation via AWS CLI
-
Log in to the AWS Management Console and click the
CloudShell icon (
>_) in the top-right corner.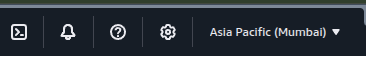
-
Enable AWS Security Hub with default security standards:
aws securityhub enable-security-hub --enable-default-standards -
Alternatively, enable AWS Security Hub without default standards:
aws securityhub enable-security-hub --no-enable-default-standards
After enabling Security Hub, findings and compliance results will begin appearing in the Security Hub dashboard.