Other Articles
- EC2 Volume – Enable EBS Encryption
- EFS – Enable EFS Storage Backup
- EC2 Instance – Enable Deletion Protection
- EC2 Instance – Monitor CPU Utilization
- ECS Service – Monitor CPU Utilization
- ECS Service – Monitor Memory Utilization
- EC2 VPC – Ensure Flow Logs are Enabled
- S3 Bucket – Block S3 Bucket Public Access
- S3 Bucket – Enable S3 Bucket Versioning
- S3 Bucket – Enable S3 Bucket Encryption
- RDS DB Instance – Enable Auto Minor Version Upgrade
- RDS DB Instance – Block Public Access
- RDS DB Instance – Monitor Free Storage Space
- RDS DB Instance – Monitor CPU Utilization
- RDS DB Instance – Encryption of Storage
- RDS DB Instance – Enable Deletion Protection
- SQS Queue – Monitor Message Age
- SQS Queue – Monitor Message Visibility
- DynamoDB Table – Enable Table Encryption
- DynamoDB Table – Enable Table Point In Time Recovery
- DynamoDB Table – Enable Table Deletion Protection
- DynamoDB Table – Monitor Table Read Capacity
- DynamoDB Table – Monitor Table Write Capacity
- DynamoDB Table – Monitor Table Latency
- Enable User MFA
- Enforce Key Rotation
- Enforce Active Key Limit
- Disable Unused User Credentials
- Enforce Group Permission
- Enable CloudTrail
- Enable AWS Security Hub
- Enforce Password Length
- Prohibit Password Reuse
- Purge Expired Certificates
- Check Root Access Keys Existence
- Enable Root MFA
- Establish Support Role
- Enable Key Rotation
- Encrypt CloudTrail Logs
- Enable GuardDuty
EC2 Volume – Enable EBS Volume Backup
This check ensures that Amazon EBS volumes are backed up using snapshots or AWS Backup. Regular backups help protect against accidental deletion, corruption, or system failures.
Check Details
- Resource: EC2 Volume
- Check: Enable EBS volume backup
- Risk: Data loss due to missing or outdated backups
Remediation via AWS Console
-
Log in to the AWS Management Console and open the Amazon EC2 console.
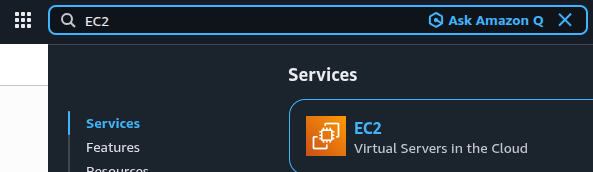
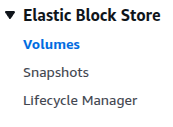
- In the left navigation pane, click Volumes under Elastic Block Store.
-
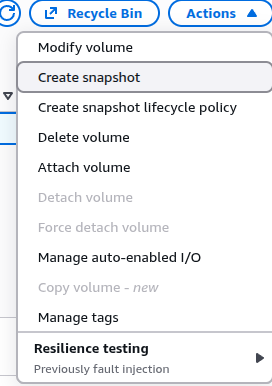
Select the EBS volume that does not have backup enabled.
-
Create a manual snapshot:
- Click Actions → Create snapshot
- Add a description
- Click Create snapshot
-
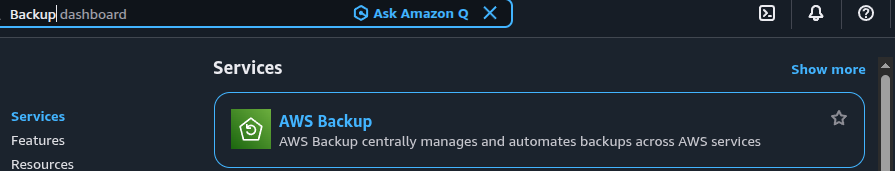
Open the AWS Backup console.
-
Choose Backup plans and click Create backup plan.
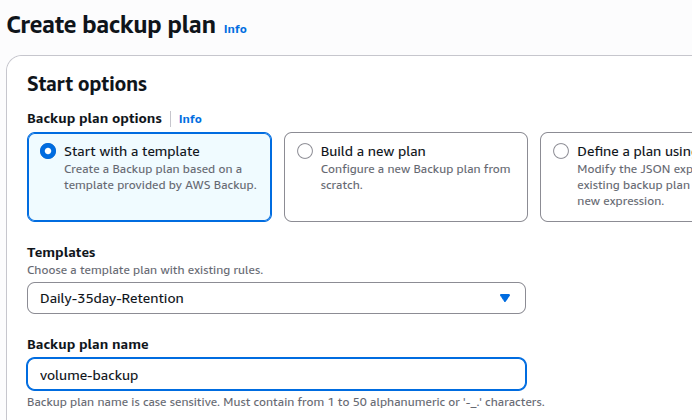
-
Add the EBS volume as a resource assignment.
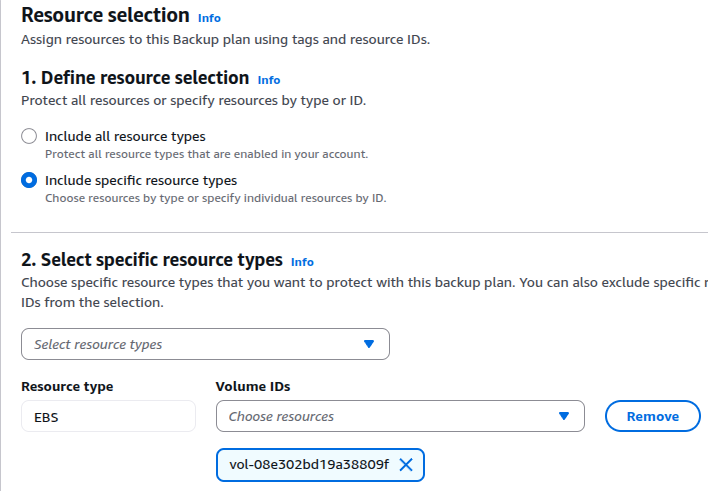
- Save the configuration.
Remediation via AWS CLI
-
Log in to the AWS Management Console and click the
CloudShell icon (
>_) in the top-right corner.
-
Create a snapshot of the EBS volume:
aws ec2 create-snapshot --volume-id <volume-id> --description "EBS backup snapshot" -
Create a backup vault:
aws backup create-backup-vault --backup-vault-name Default -
Create a backup plan:
aws backup create-backup-plan \ --backup-plan '{ "BackupPlanName": "EBS-Daily-Backup", "Rules": [{ "RuleName": "DailyBackup", "TargetBackupVaultName": "Default", "ScheduleExpression": "cron(0 12 * * ? *)", "Lifecycle": { "DeleteAfterDays": 30 } }] }' -
Assign the EBS volume to the backup plan:
aws backup create-backup-selection \ --backup-plan-id <backup-plan-id> \ --backup-selection '{ "SelectionName": "EBSVolumeSelection", "IamRoleArn": "arn:aws:iam::<aws-account-id>:role/service-role/AWSBackupDefaultServiceRole", "Resources": [ "arn:aws:ec2:<region>:<aws-account-id>:volume/<volume-id>" ] }'
Replace <backup-plan-id>, <aws-account-id>,
<volume-id>, and <region> with actual values.