Other Articles
Build Secure Network Subnet Topology
Tech Best Practices > Networking
Overview
This article explains the concept of network subnets and how they are used to organize and secure cloud infrastructure. Subnets divide a larger network into smaller, manageable segments, allowing better control over traffic, security, and resource placement.
Understanding public, private, and data subnets is essential for designing secure and scalable architectures across cloud and on-premises environments. These principles apply to major platforms such as Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP), and traditional enterprise data centers.
What is a Subnet?
A subnet (subnetwork) is a logical subdivision of a larger network, such as a Virtual Private Cloud (VPC) or Virtual Network (VNet). It allows you to group resources based on their accessibility and security requirements.
Each subnet resides within a specific availability zone and is associated with routing rules that determine how traffic flows in and out.
Types of Subnets
1. Public Subnet
A public subnet is a subnet that is directly accessible from the internet.
- Connected to an Internet Gateway (IGW)
- Has a route to the internet (0.0.0.0/0 → IGW)
- Resources can have public IP addresses
- Allows inbound and outbound internet traffic
Common use cases:
- Web servers and static websites
- Public-facing load balancers
- API gateways and edge services
- Bastion hosts (jump servers) for secure administrative access
- Content Delivery Network (CDN) origins
- Reverse proxies and web application firewalls (WAF)
- Email gateways and DNS servers
2. Private Subnet
A private subnet is not directly accessible from the internet.
- No direct route to Internet Gateway
- Typically uses NAT Gateway for outbound internet access
- Resources do not have public IPs
- More secure than public subnets
Common use cases:
- Application servers and microservices
- Backend services and business logic layers
- Internal APIs and service-to-service communication
- Containerized workloads (Docker, Kubernetes)
- Orchestration platforms and middleware
- Batch processing systems and background jobs
- CI/CD runners and automation tools
- Internal monitoring and logging systems
3. Data Subnet (Database Subnet)
A data subnet is a highly restricted subnet used for storing sensitive data.
- No internet access (inbound or outbound)
- Strict security group and network ACL rules
- Accessible only from private subnets
- Designed for maximum isolation
Common use cases:
- Relational and NoSQL databases (MySQL, PostgreSQL, MongoDB)
- Data warehouses and analytics platforms
- Caching systems (Redis, Valkey, Memcached)
- Search and indexing engines (Elasticsearch, OpenSearch)
- Message brokers and data streaming platforms
How Subnets Work Together
These subnet types work together to form a secure and scalable multi-tier network architecture.
- Public subnet handles incoming traffic from users
- Private subnet processes application logic
- Data subnet securely stores sensitive information
This layered approach ensures that critical systems are protected while still enabling necessary communication between components.
Build Secure Network Subnet Topology
- Internet → Load Balancer (Public Subnet)
- Load Balancer → Application Server (Private Subnet)
- Application Server → Database (Data Subnet)
This design minimizes exposure and follows industry-standard security best practices.
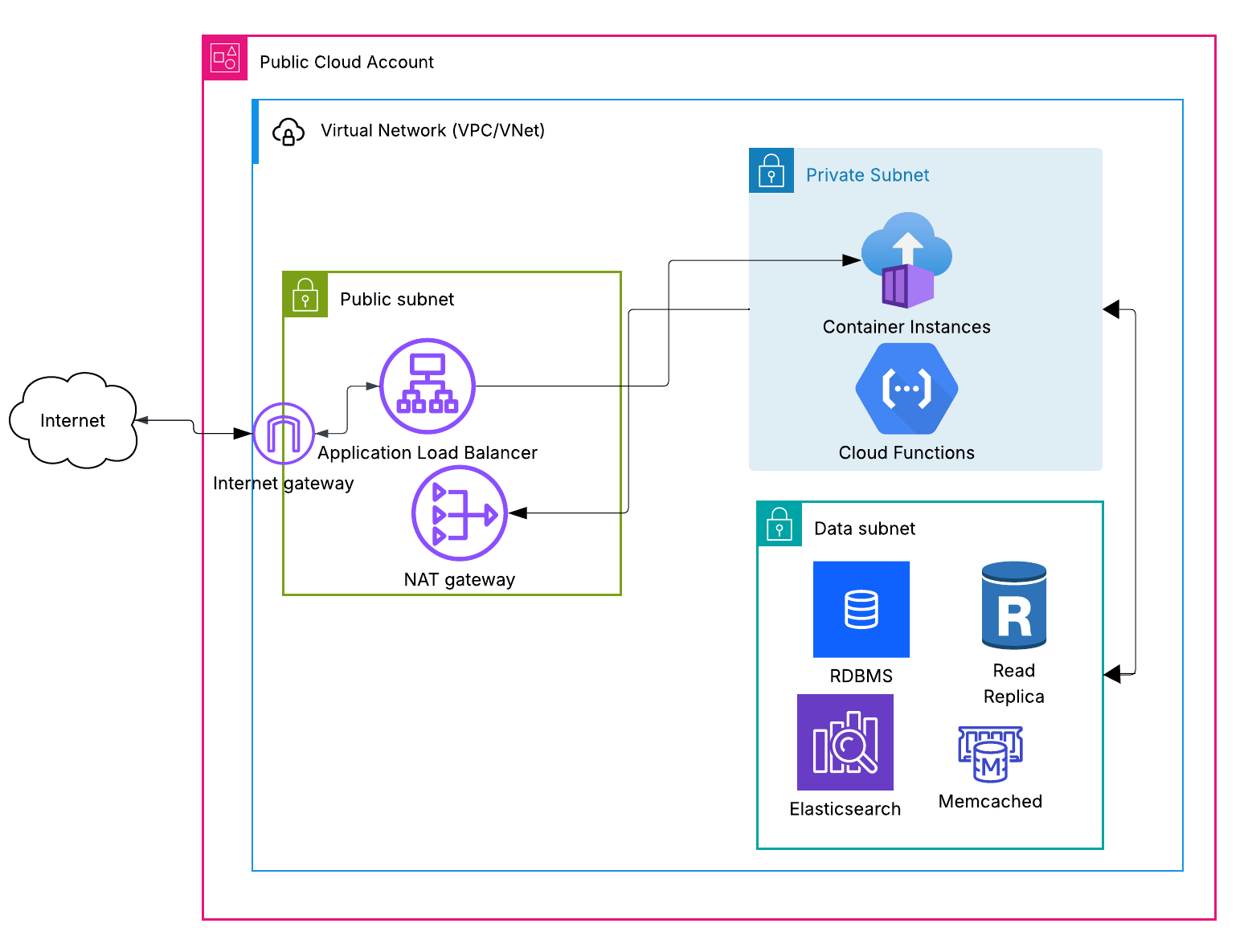
Figure: A secure three-tier network architecture illustrating Public, Private, and Data Subnets within a virtual network across cloud environments.
Benefits of Using Subnets
- Improved security through network isolation
- Better traffic management and routing control
- Scalability across multiple availability zones
- Clear separation of responsibilities within architecture
Best Practices
- Do not place databases in public subnets
- Use a NAT Gateway or NAT service for controlled outbound access
- Apply least privilege access using security groups
- Separate application and data layers
- Use multiple availability zones for high availability
Common Mistakes to Avoid
- Exposing sensitive resources to public subnets
- Misconfiguring route tables
- Allowing unrestricted access between subnets
- Using the same subnet for all resources
- Ignoring network segmentation
Updated on 27 March, 2026