Other Articles
AWS CloudTrail: API Logging and Activity Monitoring
Tech Best Practices > Security
Overview
AWS CloudTrail is a logging and monitoring service that records all API activity and user actions across your AWS environment.
It provides visibility into who did what, when, and from where, enabling auditing, compliance, and security analysis.
CloudTrail operates continuously and helps detect unauthorized access, configuration changes, and suspicious activity.
What is AWS CloudTrail?
AWS CloudTrail is a fully managed service that captures and logs API calls made in your AWS account by users, services, and applications.
It records activity across AWS services such as EC2, IAM, S3, and more, providing a complete audit trail of actions performed in your environment.
How CloudTrail Works
- Captures API calls from AWS services and users
- Records details such as user identity, timestamp, and source IP
- Stores logs securely in Amazon S3
- Integrates with CloudWatch for monitoring and alerts
- Provides logs for auditing, compliance, and troubleshooting
Key Features
- Complete API activity logging
- Secure log storage in Amazon S3
- Integration with CloudWatch and EventBridge
- Supports multi-region tracking
- Enables compliance and auditing
Types of Events in CloudTrail
1. Management Events
- IAM changes
- EC2 instance operations
- Security group updates
2. Data Events
- S3 object access
- Lambda function execution
- DynamoDB operations
3. Insights Events
- Unusual API activity spikes
- Abnormal user behavior
CloudTrail Logging Flow
- User / Service performs action
- CloudTrail records API call
- Logs stored in Amazon S3
- Events sent to CloudWatch / EventBridge
- Alerts and monitoring configured
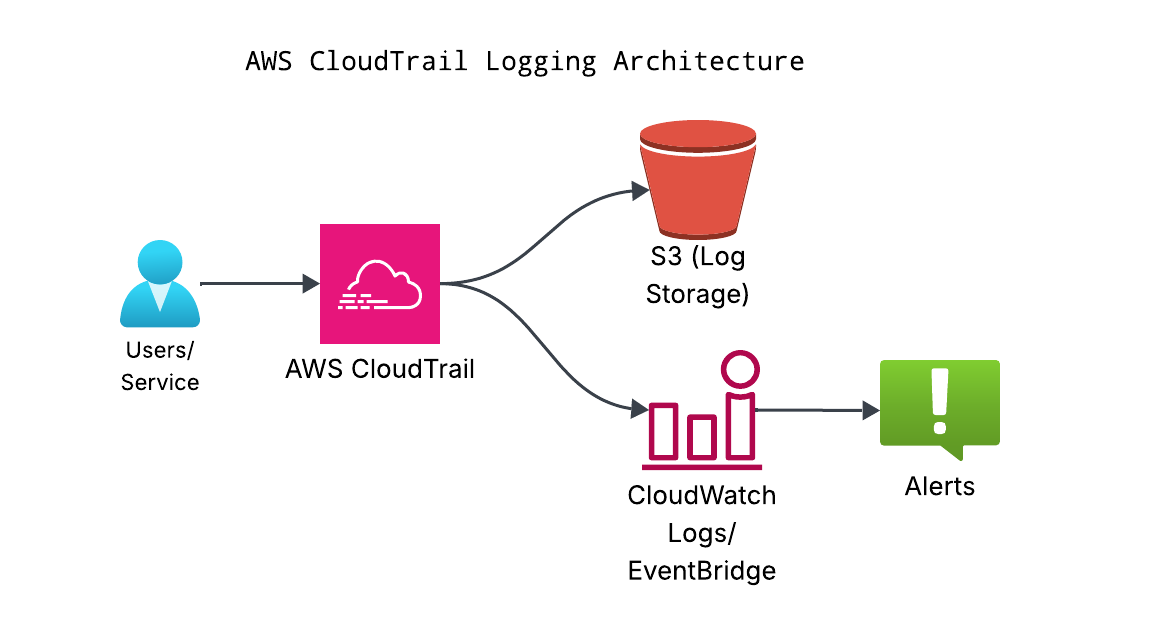
Figure: AWS CloudTrail records API activity and enables monitoring and auditing.
Benefits of Using CloudTrail
- Complete visibility into AWS activity
- Improved security and auditing
- Helps meet compliance requirements
- Supports incident investigation
- Centralized logging across AWS services
Best Practices
- Enable CloudTrail in all regions
- Store logs in a secure S3 bucket with encryption
- Enable log file validation
- Integrate with CloudWatch for alerting
- Restrict access to logs using IAM policies
Common Mistakes to Avoid
- Not enabling CloudTrail across all regions
- Not securing S3 log storage
- Ignoring logs and alerts
- Not enabling log validation
- Overlooking integration with monitoring tools
Updated on 22 April, 2026