Other Articles
Enable AWS GuardDuty for Threat Detection
Tech Best Practices > Security
Overview
AWS GuardDuty is a threat detection service that continuously monitors your AWS environment for malicious activity and unauthorized behavior. It uses machine learning, anomaly detection, and threat intelligence feeds to identify potential security risks.
GuardDuty helps organizations improve security posture without managing complex infrastructure. It analyzes logs such as VPC Flow Logs, CloudTrail events, and DNS logs to detect threats in real time.
GuardDuty operates without requiring agents or additional infrastructure, making it easy to enable across AWS accounts.
What is AWS GuardDuty?
AWS GuardDuty is a fully managed security service designed to detect threats and suspicious activity in your AWS accounts and workloads.
It uses machine learning and threat intelligence from AWS and leading third parties to help protect your AWS accounts, workloads, and data from threats.
How GuardDuty Works
- Analyzes CloudTrail logs for API activity
- Monitors VPC Flow Logs for network traffic anomalies
- Checks DNS logs for suspicious domain requests
- Uses threat intelligence feeds to detect known malicious IPs
- Applies machine learning to identify unusual behavior patterns
- Generates findings with severity levels and actionable insights
Key Features
- Continuous threat detection
- No infrastructure to manage
- Built-in threat intelligence
- Integration with AWS Security Hub and EventBridge (CloudWatch)
- Real-time alerts and findings
Types of Threats Detected
1. Unauthorized Access
- Compromised IAM credentials
- Suspicious API calls
- Login attempts from unusual locations
2. Instance Compromise
- Communication with malicious IPs
- Crypto-mining activity
- Port scanning behavior
3. Data Exfiltration
- Unusual data transfer patterns
- Access to sensitive resources
- Large outbound traffic spikes
GuardDuty in a Secure Architecture
- Logs generated → CloudTrail, VPC, DNS
- GuardDuty analyzes logs
- Findings generated for suspicious activity
- Findings are sent to Security Hub for centralized visibility and to EventBridge (CloudWatch) for alerting
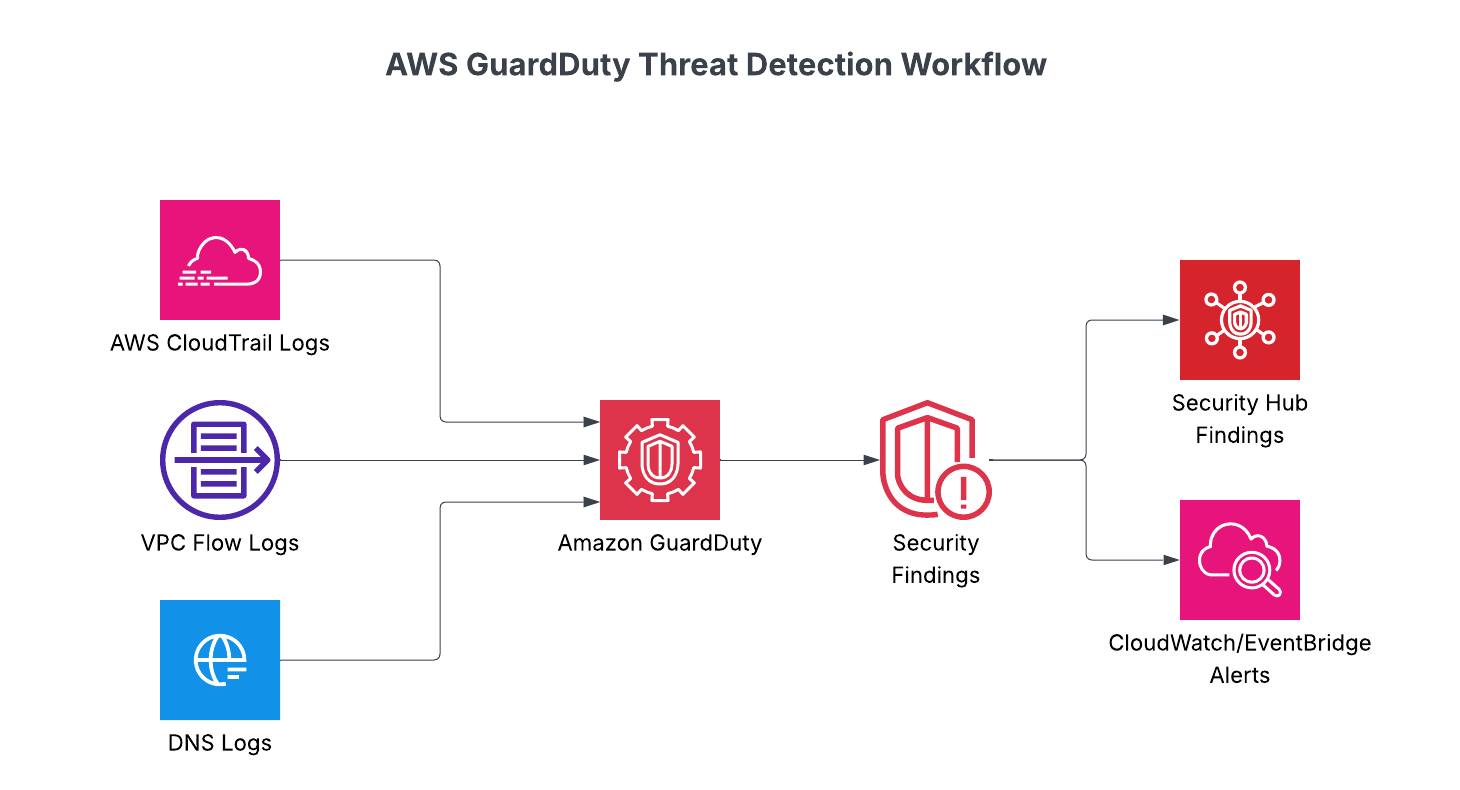
Figure: AWS GuardDuty analyzes multiple log sources and generates actionable security findings.
Benefits of Using GuardDuty
- Continuous Monitoring
- Machine learning-powered threat detection
- Enables faster incident detection and response
- Scalable, fully managed threat detection
- End-to-end visibility into AWS compute workloads
Best Practices
- Enable GuardDuty across all AWS accounts using AWS Organizations
- Enable GuardDuty in all regions
- Integrate with Security Hub for centralized monitoring
- Set up alerting using CloudWatch
- Regularly review findings
- Use IAM least privilege policies
Common Mistakes to Avoid
- Not enabling GuardDuty in all regions
- Ignoring security findings
- Not configuring alert notifications
- Overlooking integration with other security services
- Assuming GuardDuty replaces all security tools
Updated on 22 April, 2026