Other Articles
- SQL Database – Enable Database Encryption
- SQL Server – Enable SQL Defender
- SQL Database – Monitor CPU Utilization
- SQL Database – Monitor IO Utilization
- SQL Database – Monitor Memory Utilization
- SQL Database – Protect From Direct Internet Traffic
- Storage Account – Enable Storage Encryption
- Storage Account – Disable Blob Public Access
- Storage Account – Disable Cross-Tenant Replication
- Storage Account – Disable Public Network Access
- Storage Account – Enable Microsoft Defender
- Storage Account – Enable Secure Transfer
- Storage Account – Enforce Minimum TLS Version
- Storage Account – Enforce Network Access Rule
- Storage Account – Enforce Private Endpoint Access
- User – Enable Azure MFA
- App Service – Disable Remote Debugging
- App Service – Enable Defender
- App Service – Enable Entra ID Registration
- App Service – Enable HTTP2
- App Service – Enforce Latest TLS Version
- App Service – Enforce Secure FTPS State
- App Service – Redirect HTTP to HTTPS
- Cosmos DB – Enable Backup
- Cosmos DB – Enable Microsoft Defender
- Cosmos DB – Monitor Latency
- Cosmos DB – Ensure Private Connectivity
- Cosmos DB for PostgreSQL – Monitor CPU Utilization
- Cosmos DB for PostgreSQL – Monitor IO Utilization
- Cosmos DB for PostgreSQL – Monitor Memory Utilization
- Cosmos DB for PostgreSQL – Protect From Direct Internet Traffic
- Cosmos DB – Protect From Direct Internet Traffic
- Cosmos DB – Restrict Firewall Network Access
- Virtual Machine – Enable Defender
- Virtual Machine – Protect From Direct Internet Traffic
- Key Vault – Enable Defender
- Key Vault – Ensure Vault Recoverable
- Key Vault – Require Private Endpoint Access
- MySQL Flexible Server – Enable Audit Log Events Connection
- MySQL Flexible Server – Enable Audit Logs
- MySQL Flexible Server – Enforce Minimum TLS Version
- PostgreSQL Flexible Server – Configure Log File Retention
- PostgreSQL Flexible Server – Enable Connection Logging
- PostgreSQL Flexible Server – Enable Connection Throttling
- PostgreSQL Flexible Server – Enable Disconnection Logging
- PostgreSQL Flexible Server – Enable Log Checkpoints
- Network Security Group – Ensure Flow Logs Captured
- General – Enable Auto Provisioning Log Analytics
- General – Enable Security Notifications
- General – Set Additional Email Address
App Service – Monitor Server Errors
This check ensures that server errors are actively monitored for Azure Web Apps. Monitoring server-side errors helps quickly detect availability issues, application crashes, and backend failures that may impact users.
Check Details
- Resource: Azure App Service (Web App)
- Check: Ensure Server Errors Are Monitored
- Risk: Without monitoring server errors, application failures may go undetected, leading to downtime, degraded performance, and poor user experience.
Remediation via Azure Portal
-
Log in to the Azure Portal.
-
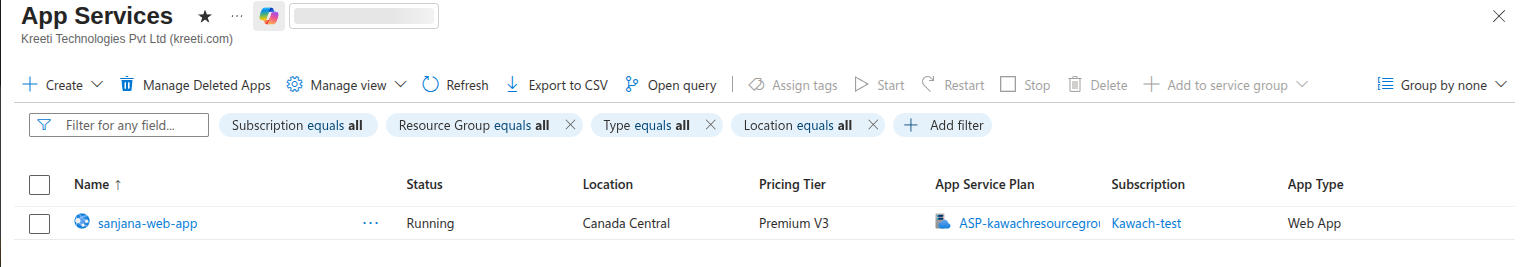
Navigate to App Services and select your Web App.
-
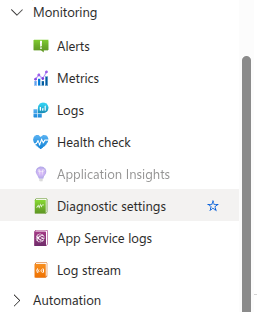
In the left menu, select Monitoring → Diagnostic settings.
-
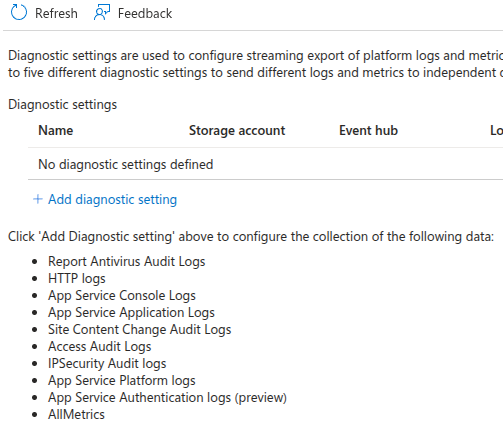
Click Add diagnostic setting.
-
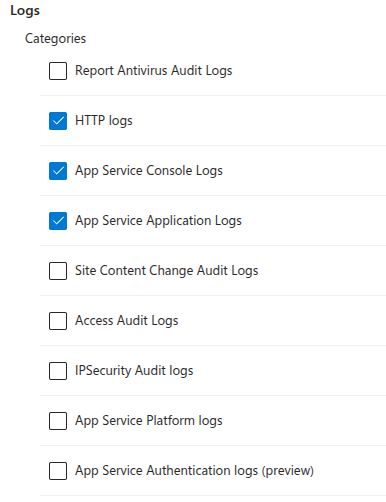
Enable logging for:
- AppServiceHTTPLogs
- AppServiceConsoleLogs
- AppServiceAppLogs
-
Configure a destination such as:
- Log Analytics Workspace
- Storage Account
- Event Hub
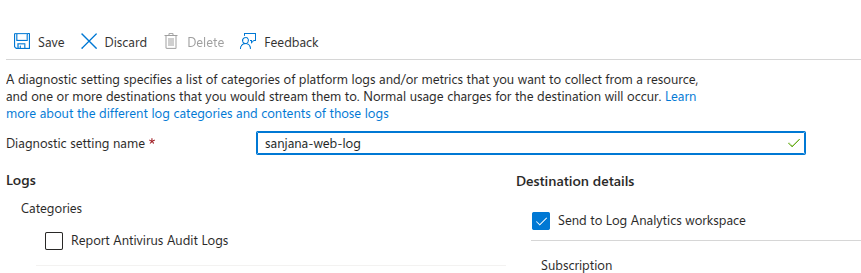
- Click Save to enable monitoring.
Remediation via Azure CLI
-
Open Azure Cloud Shell or a local terminal with Azure CLI installed.

- Create a diagnostic setting for the Web App:
- Verify diagnostic settings:
az monitor diagnostic-settings create \
--name "webapp-error-monitoring" \
--resource <web-app-resource-id> \
--workspace <log-analytics-workspace-id> \
--logs '[{"category":"AppServiceHTTPLogs","enabled":true},
{"category":"AppServiceConsoleLogs","enabled":true},
{"category":"AppServiceAppLogs","enabled":true}]'
az monitor diagnostic-settings list \ --resource <web-app-resource-id>
Replace <web-app-resource-id> and
<log-analytics-workspace-id> with your actual resource values.