Other Articles
- SQL Database – Enable Database Encryption
- SQL Server – Enable SQL Defender
- SQL Database – Monitor CPU Utilization
- SQL Database – Monitor IO Utilization
- SQL Database – Monitor Memory Utilization
- SQL Database – Protect From Direct Internet Traffic
- Storage Account – Enable Storage Encryption
- Storage Account – Disable Blob Public Access
- Storage Account – Disable Cross-Tenant Replication
- Storage Account – Disable Public Network Access
- Storage Account – Enable Microsoft Defender
- Storage Account – Enable Secure Transfer
- Storage Account – Enforce Minimum TLS Version
- Storage Account – Enforce Network Access Rule
- Storage Account – Enforce Private Endpoint Access
- User – Enable Azure MFA
- App Service – Disable Remote Debugging
- App Service – Enable Defender
- App Service – Enable Entra ID Registration
- App Service – Enable HTTP2
- App Service – Enforce Latest TLS Version
- App Service – Enforce Secure FTPS State
- App Service – Monitor Server Errors
- App Service – Redirect HTTP to HTTPS
- Cosmos DB – Enable Backup
- Cosmos DB – Enable Microsoft Defender
- Cosmos DB – Monitor Latency
- Cosmos DB – Ensure Private Connectivity
- Cosmos DB for PostgreSQL – Monitor CPU Utilization
- Cosmos DB for PostgreSQL – Monitor IO Utilization
- Cosmos DB for PostgreSQL – Monitor Memory Utilization
- Cosmos DB – Protect From Direct Internet Traffic
- Cosmos DB – Restrict Firewall Network Access
- Virtual Machine – Enable Defender
- Virtual Machine – Protect From Direct Internet Traffic
- Key Vault – Enable Defender
- Key Vault – Ensure Vault Recoverable
- Key Vault – Require Private Endpoint Access
- MySQL Flexible Server – Enable Audit Log Events Connection
- MySQL Flexible Server – Enable Audit Logs
- MySQL Flexible Server – Enforce Minimum TLS Version
- PostgreSQL Flexible Server – Configure Log File Retention
- PostgreSQL Flexible Server – Enable Connection Logging
- PostgreSQL Flexible Server – Enable Connection Throttling
- PostgreSQL Flexible Server – Enable Disconnection Logging
- PostgreSQL Flexible Server – Enable Log Checkpoints
- Network Security Group – Ensure Flow Logs Captured
- General – Enable Auto Provisioning Log Analytics
- General – Enable Security Notifications
- General – Set Additional Email Address
Cosmos DB for PostgreSQL – Protect From Direct Internet Traffic
This check ensures that Azure Cosmos DB for PostgreSQL clusters are not directly exposed to the public internet. Deploying clusters within private virtual networks and restricting public access reduces the risk of unauthorised access and external threats.
Check Details
- Resource: Azure Cosmos DB for PostgreSQL
- Check: Ensure Protection From Direct Internet Traffic
- Risk: If public network access is enabled or firewall rules allow unrestricted access (such as 0.0.0.0/0), the PostgreSQL cluster may be exposed to brute-force attacks, unauthorized connections, and potential data compromise.
Remediation via Azure Portal
-
Log in to the Azure Portal.
-
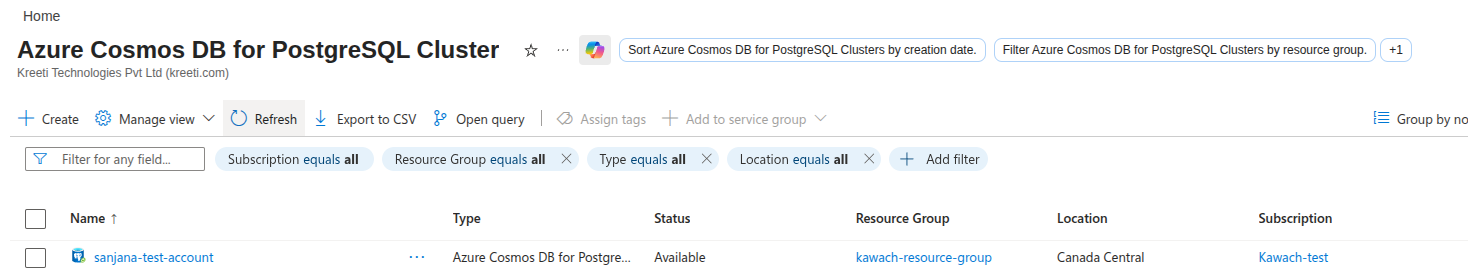
Navigate to Azure Cosmos DB for PostgreSQL and select the affected cluster.
-
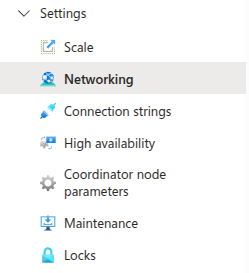
Under Settings, select Networking.
-
Ensure Public access is set to Disabled.
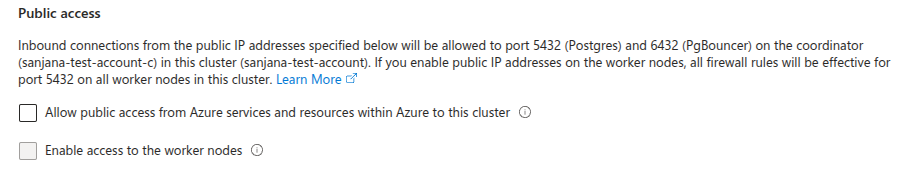
- If public access is required, ensure firewall rules restrict access to specific trusted IP address ranges only.
- Confirm the cluster is deployed within a Virtual Network (VNet) for private connectivity.
- Click Save to apply the configuration.
Remediation via Azure CLI
-
Open Azure Cloud Shell or a local terminal with Azure CLI installed.

-
Disable public network access for the PostgreSQL cluster:
az postgres flexible-server update \ --resource-group <resource-group> \ --name <cluster-name> \ --public-access none
-
Verify that public access is disabled:
az postgres flexible-server show \ --resource-group <resource-group> \ --name <cluster-name> \ --query publicNetworkAccess
The output should return "Disabled", confirming that the PostgreSQL cluster is protected from direct internet traffic.