Other Articles
- Cloud SQL – Configure Private IP
- Cloud SQL – Monitor CPU Utilization
- Cloud SQL – Enable Deletion Protection
- Cloud SQL – Enable Disk Encryption
- Cloud SQL – Enable Automated Backups
- Cloud SQL – Enable Log Export
- Cloud SQL – Enforce Password Validation
- Cloud SQL – Enforce Secure Transport
- Compute Engine – Block Project-Wide SSH Keys
- Compute Engine – Disable IP Forwarding
- Compute Engine – Disable Public IP Addresses
- Compute Engine – Disable Serial Port Access
- Compute Engine – Enable Confidential Computing
- Compute Engine – Enable OS Login
- Compute Engine – Enable Shielded VM
- Compute Engine – Restrict Default Service Account
- General – Deny Public Access to KMS Keys
- General – Enforce Duties Separation
- General – Enforce KMS Key Rotation
- General – Restrict Admin Roles on Service Accounts
- Cloud Run – Configure Timeout Settings
- Cloud Storage – Enable Bucket Encryption
- Cloud Storage – Enable Bucket Logging
- Cloud Storage – Enable Bucket Versioning
- Cloud Storage – Enforce Uniform Bucket-Level Access
- Cloud Storage – Restrict Public Access
- IAM Users – Enforce GCP-Managed Keys
- IAM Users – Rotate External User-Managed Service Account Keys
Cloud SQL – Protect From Internet Access
This check ensures that Cloud SQL instances are protected from direct internet access. Restricting public exposure reduces the risk of unauthorized access, network-based attacks, and data breaches.
Check Details
- Resource: Cloud SQL
- Check: Protect from direct internet access
- Risk: If Cloud SQL instances are directly accessible from the internet, attackers may attempt brute-force attacks, exploit vulnerabilities, or gain unauthorized access to sensitive data.
Remediation via Google Cloud Console
-
Log in to the Google Cloud Console and navigate to
Cloud SQL.
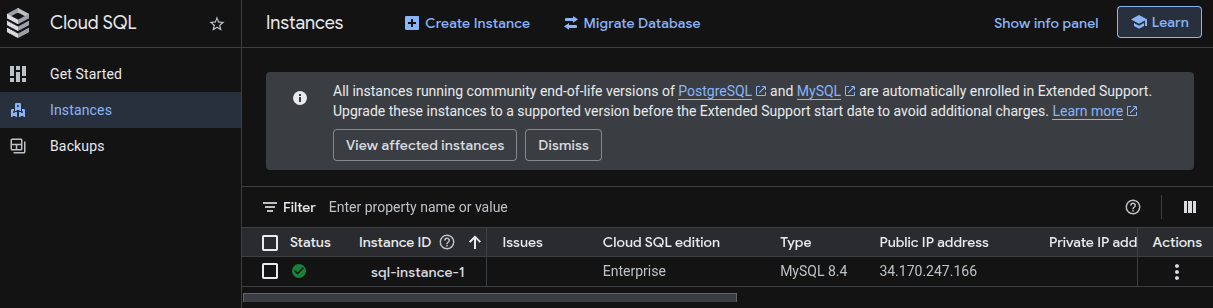
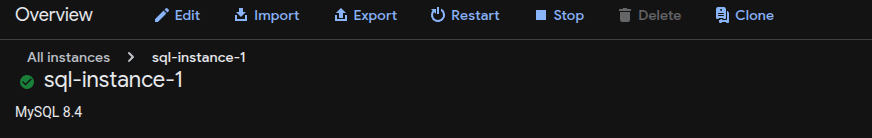
- Click on the affected Cloud SQL instance.
-
Click Edit to modify the instance configuration.
- Scroll to the Connections section.
-
Under Public IP, ensure that public IP access is
disabled or that no authorized networks are configured.
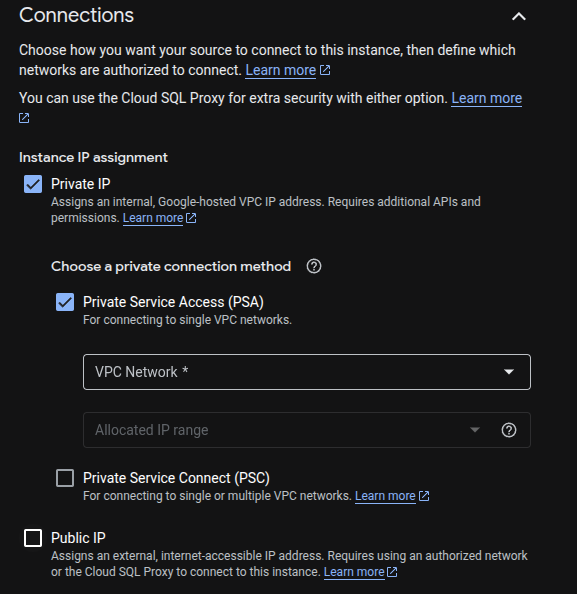
- Click Save to apply the changes.
Remediation via Google Cloud CLI
-
Open the Google Cloud Console and launch
Cloud Shell.
-
Disable public IP access for the Cloud SQL instance:
gcloud sql instances patch <INSTANCE_NAME> \ --no-assign-ip
Replace <INSTANCE_NAME> with your Cloud SQL instance name.
Disabling public IP ensures the instance cannot be accessed directly from the
internet.
Default Value
By default, Cloud SQL instances may have public IP enabled, allowing direct internet access unless explicitly restricted during instance configuration.